Function security is the mechanism by which user access to applications functionality is controlled.
Function security can be considered as “global data security”, in that it grants access to a function regardless of the current row of data. Oracle Applications architecture aggregates several related business functions into a single form. Because all users should not have access to every business function in a form, Oracle Applications provides the ability to identify pieces of applications logic as functions. When part of an application’s functionality is identified as a function, it can be secured (i.e., included or excluded from a responsibility).
Application developers register functions when they develop forms. A System Administrator administers function security by creating responsibilities that include or exclude particular functions.
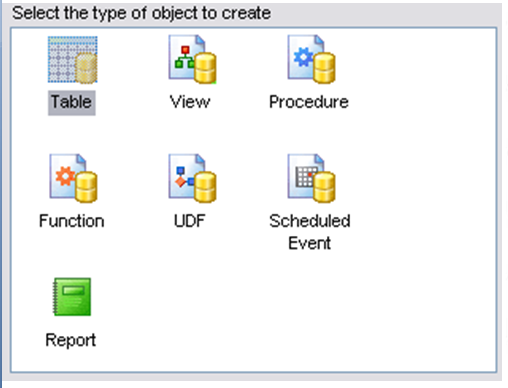
FunctionA function is a part of an application’s functionality that is registered under a unique name for the purpose of assigning it to, or excluding it from, a responsibility. There are two types of functions: executable functions (formerly called form functions), and non-executable functions (formerly called subfunctions).
Executable FunctionExecutable functions have the unique property that you may navigate to them using the Navigate window.
Non-executable FunctionA non-executable function) is a securable subset of a form’s functionality: in other words, a function executed from within a form.
A developer can write a form to test the availability of a particular non-executable function, and then take some action based on whether the non-executable function is available in the current responsibility.
Non-executable functions are frequently associated with buttons or other graphical elements on forms. For example, when a non-executable function is enabled, the corresponding button is enabled.
However, a non-executable function may be tested and executed at any time during a form’s operation, and it need not have an explicit user interface impact. For example, if a non-executable function corresponds to a form procedure not associated with a graphical element, its availability is not obvious to the form’s user.
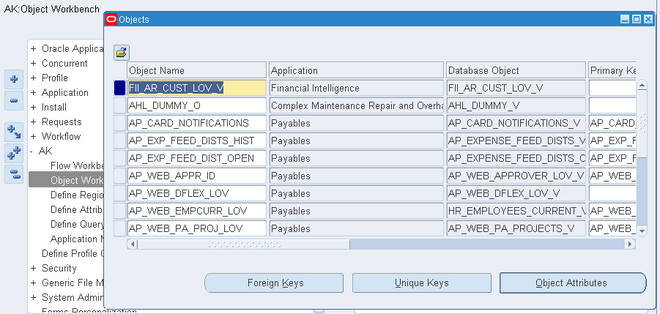
MenuA menu is a hierarchical arrangement of functions and menus of functions. Each responsibility has a menu assigned to it.
Menus can map to permission sets as well.
Menu EntryA menu entry is a menu component that identifies a function or a menu of functions. In some cases, both a function and a menu of functions correspond to the same menu entry. For example, both a form and its menu of subfunctions can occupy the same menu entry
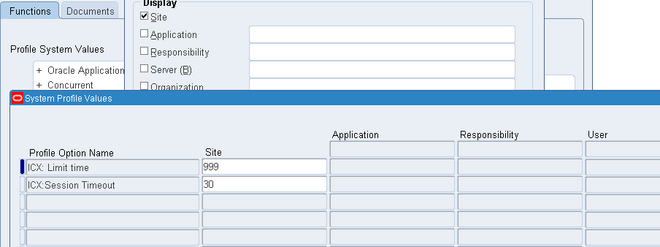
ResponsibilityA responsibility defines an application user’s current privileges while working with Oracle Applications. When an application user signs on, they select a responsibility that grants certain privileges, specifically:
- The functions that the user may access. Functions are determined by the menu assigned to the responsibility.
- The concurrent programs, such as reports, that the user may run.
- The application database accounts that forms, concurrent programs, and reports connect to.

Recent Comments