Access Control with Oracle User Management
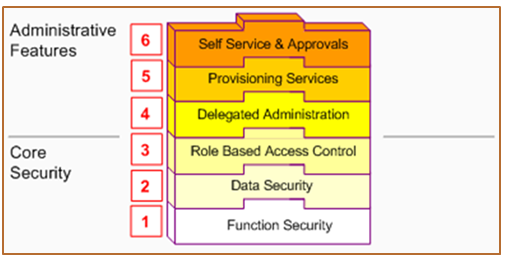
In Release 12 Core Security includes Oracle’s Function and Data Security models, as well as Role Based Access Control. Administrative Features build upon Core Security and include Delegated Administration, Registration Processes, and Self Service and Approvals.
Core Security and Administrative Features are implemented in successive layers and each builds upon the one that precedes it. Organizations can optionally uptake the various layers, depending on the degree of automation and scalability that they wish to build upon the existing Function and Data Security models.
In general, Access Control with Oracle User Management begins with basic system administration tasks, progresses to more distributed, local modes of administration, and ultimately enables users to perform some basic, predefined registration tasks on their own. The above diagram illustrates how the layers build upon each other.
Function Security
Function Security is the base layer of access control in Oracle Applications. It restricts user access to individual menus and menu options within the system, but does not restrict access to the data contained within those menus. For example, an organization could use Function Security to provide its sales representatives with the required
menus and menu options for querying customers. It could also control access to specific components of those pages such as a button on a sales forecasting page
Data Security
Data Security is the next layer of access control. Building on Function Security, Data Security provides access control within Oracle Applications on the data a user can access, and the actions a user can perform on that data. Oracle Applications restricts access to individual data that is displayed on the screen once the user has selected a menu or menu option. For example, Data Security restricts the set of users that a local administrator can access within Oracle User Management. Data Security policies can only be defined for applications that have been written to utilize the Data Security Framework.
Role Based Access Control (RBAC)
RBAC is the next layer and builds upon Data Security and Function Security. With RBAC, access control is defined through roles, and user access to Applications is determined by the roles granted to the user. Access control in Oracle Applications closely follows the RBAC ANSI standard (ANSI INCITS 359-2004) originally proposed by the National Institute of Standards & Technology (NIST), which defines a role as “a job function within the context of an organization with some associated semantics regarding the authority and responsibility conferred on the user assigned to the role.”
A role can be configured to consolidate the responsibilities, permissions, function security and data security polices that users require to perform a specific function. This is accomplished with a one-time setup, in which permissions, responsibilities, and other roles are assigned to the role. Users are not required to be assigned the lower-level
permissions directly, since permissions are implicitly inherited on the basis of the roles assigned to the user. This simplifies mass updates of user permissions, since an organization need only change the permissions or role inheritance hierarchy defined for a given role, and the users assigned that role will inherit the new set of permissions
automatically.
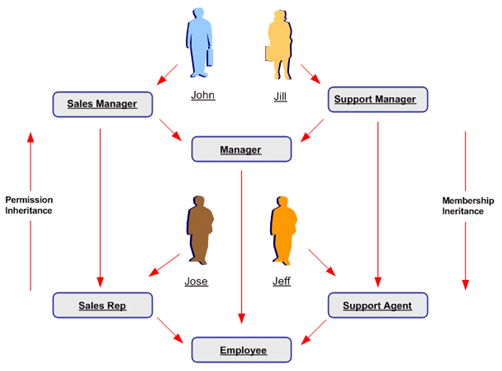
Role Inheritance Hierarchies
Roles can be included in role inheritance hierarchies that can contain multiple subordinate roles and superior roles. With role inheritance hierarchies, a superior role inherits all of the properties of its subordinate role, as well as any of that role’s own subordinate roles. The following example demonstrates how role inheritance hierarchies can greatly simplify user access control and administration.
Delegated Administration is a privilege model that builds on the RBAC system to provide organizations with the ability to assign the required access rights for managing roles and user accounts. With delegated administration, instead of relying on a central administrator to manage all its users, an organization can create local administrators and grant them sufficient privileges to manage a specific subset of the organization’s users and roles. This provides organizations with a tighter, more granular level of security, and the ability to easily scale their administrative capabilities. For example, organizations could internally designate administrators at division or even department
levels, and then delegate administration of external users to people within those (external) organizations. Delegation policies are defined as data security policies. The set of data policies that are defined as part of delegated administration are known as Administration Privileges.
Delegating to Proxy Users
There are a number of business scenarios in which users of Oracle E-Business Suite need to grant delegates the ability to act on their behalf (act as proxy users for them) when performing specific E-Business Suite functions. Traditionally, delegators have done this by giving passwords for specific applications to other users. A delegate who
was given another user’s passwords for certain applications could assume the identity and privileges of the delegator within those applications, and only those applications.
The integration of E-Business Suite with Oracle Application Server 10g Single Sign-On (SSO) makes this traditional strategy insecure. If a delegator grants a delegate access to his SSO password, the delegate will be able to access every SSO-enabled application to which the delegator has access, not just to specific applications. The new mechanism was designed to enable limited, auditable delegation of privilege from delegators to their delegate
Provisioning Services
Provisioning services are modeled as registration processes that enable end users to perform some of their own registration tasks, such as requesting new accounts or additional access to the system. They also provide administrators with a faster and more efficient method of creating new user accounts, as well as assigning roles.
Registration processes accomplish this by encapsulating core components of registration, including:
- The role(s) assigned after the user successfully completes the process.
- An optional registration user interface for collecting account or additional information.
- A workflow for approval, confirmation, rejection, and identity verification notifications.
- The Approval Management Transaction Type. A transaction type represents a set of approval routing rules that are interpreted at runtime.
- The set of users that are eligible to sign up for additional access (only applicable for Request for Additional Access registration processes).
- Whether identity verification is required. Identity verification confirms the identity of a requester before the registration request is processed, by sending an email notification to the requester’s email address. If the recipient does not reply within a specified time, the request will be automatically rejected.
- The set of local administrators that should be able to register people and/or create users through the Account Creation by Administrators registration process.
When a user completes registration using a registration process, the system captures the required information from the user, and subsequently assigns that person a new user account, role, or both. Oracle User Management supports three types of registration processes: Self-service Account Requests, Requests for Additional Access, and Account Creation by Administrators.
Leave a Reply
Want to join the discussion?Feel free to contribute!